Cybercriminals aren’t just going after big targets anymore.
They’re going after everyone, and they’re doing it with infostealer malware. These small, sneaky programs are quietly stealing passwords, browser data and login tokens from everyday devices.
A new report shows just how out of control the problem has become, with infostealer activity jumping 500% in just one year, harvesting more than 1.7 billion fresh credentials.
Join the FREE “CyberGuy Report”: Get my expert tech tips, critical security alerts and exclusive deals, plus instant access to my free “Ultimate Scam Survival Guide” when you sign up!
The industrialization of credential theft
In 2024, cybersecurity researchers at Fortinet observed a staggering surge in stolen login data being traded on the dark web. Over 1.7 billion credentials were harvested not from old breaches but through active infections on users’ devices.
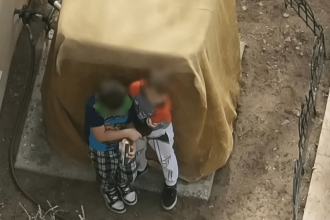
At the heart of this epidemic is a class of malware called infostealers, which are programs designed specifically to extract sensitive information like usernames, passwords, browser cookies, email logins, crypto wallets and session tokens. Unlike large-scale data breaches that target centralized databases, infostealers operate on individual machines. They don’t break into a company’s servers; they compromise the end user, often without the victim ever noticing.
These logs are then aggregated and sold by initial access brokers, intermediaries who sell compromised credentials and access tokens to other cybercriminal groups, including ransomware operators. The market has matured to the point where access to a corporate VPN, an admin dashboard or even a personal bank account can be purchased at scale, with verified functionality and region-specific pricing.
Fortinet’s 2025 Global Threat Landscape Report identified a 500% increase in credential logs from infostealer infections over the past year. Among the most widespread and dangerous infostealers identified in the report are RedLine, Vidar and Raccoon.

200 MILLION SOCIAL MEDIA RECORDS LEAKED IN MAJOR X DATA BREACH
How infostealers work
Infostealers are typically distributed through phishing emails, malicious browser extensions, fake software installers or cracked applications. Once installed on a device, they scan browser databases, autofill records, saved passwords and local files for any credential-related data. Many also look for digital wallets, FTP credentials and cloud service logins.
Crucially, many infostealers also exfiltrate session tokens and authentication cookies, meaning that even users who rely on multifactor authentication are not entirely safe. With a stolen session token, an attacker can bypass multifactor authentication entirely and assume control of the session without ever needing to log in manually.
Once collected, the data is uploaded to a command and control server. From there, it’s either used directly by attackers or bundled into logs and sold on forums. These logs can include everything from the victim’s IP address and geolocation to their browser fingerprint and full credential list, giving attackers everything they need to carry out further exploitation or impersonation.
WHAT IS ARTIFICIAL INTELLIGENCE (AI)?

HR FIRM CONFIRMS 4M RECORDS EXPOSED IN MAJOR HACK
5 ways to stay safe from infostealer malware
With infostealer malware becoming a growing threat, protecting your data requires a mix of smart security habits and reliable tools. Here are five effective ways to keep your information safe.
1. Use a password manager: Many infostealers target saved passwords in web browsers. Instead of relying on your browser to store credentials, use a dedicated password manager. Our No. 1 pick has a built-in Data Breach Scanner that lets you check if your information has been exposed in known breaches. Get more details about my best expert-reviewed Password Managers of 2025 here.
2. Enable two-factor authentication (2FA): Even if your credentials are stolen, 2FA adds an extra layer of security by requiring a second form of verification, such as a code from an authentication app or biometric confirmation. Cybercriminals rely on stolen usernames and passwords to break into accounts, but with 2FA enabled, they cannot gain access without the additional security step. Make sure to enable 2FA on important accounts like email, banking and work-related logins.
3. Use strong antivirus software and be cautious with downloads and links: Infostealer malware often spreads through malicious downloads, phishing emails and fake websites. Avoid downloading software or files from untrusted sources and always double-check links before clicking them. Attackers disguise malware as legitimate software, game cheats or cracked applications, so it is best to stick to official websites and app stores for downloads.
The best way to safeguard yourself from malicious links that install malware, potentially accessing your private information, is to have strong antivirus software installed on all your devices. This protection can also alert you to phishing emails and ransomware scams, keeping your personal information and digital assets safe. Get my picks of the best 2025 antivirus protection winners for your Windows, Mac, Android and iOS devices.
4. Keep software updated: Cybercriminals exploit outdated software to deliver malware. Keeping your operating system, browsers and security software up to date ensures that known vulnerabilities are patched. Enable automatic updates whenever possible and install reputable antivirus or endpoint protection software that can detect and block infostealer threats before they compromise your system.
5. Consider a personal data removal service: These services can help remove your personal information from data broker sites, reducing your risk of identity theft, spam and targeted scams. While no service can guarantee the complete removal of your data from the internet, a data removal service is really a smart choice. They aren’t cheap, and neither is your privacy.
These services do all the work for you by actively monitoring and systematically erasing your personal information from hundreds of websites. It’s what gives me peace of mind and has proven to be the most effective way to erase your personal data from the internet. By limiting the information available, you reduce the risk of scammers cross-referencing data from breaches with information they might find on the dark web, making it harder for them to target you. Check out my top picks for data removal services here.
HOW TO FIGHT BACK AGAINST DEBIT CARD HACKERS WHO ARE AFTER YOUR MONEY
Kurt’s key takeaway
The 1.7 billion passwords leaked in 2024 are not a relic of past breaches. They’re evidence of an evolving, industrialized cybercrime economy built on the backs of unsuspecting users and quietly infected devices. The tools are cheap, the scale is massive and the impact is personal. If you’ve ever saved a password in a browser, downloaded an unofficial app or clicked a link in a sketchy email, your credentials may already be in circulation.
Who do you think should be primarily responsible for protecting personal and organizational data from cyber threats: individual users, companies, software providers or government agencies? Why? Let us know by writing us at Cyberguy.com/Contact.
For more of my tech tips and security alerts, subscribe to my free CyberGuy Report Newsletter by heading to Cyberguy.com/Newsletter.
Ask Kurt a question or let us know what stories you’d like us to cover.
Follow Kurt on his social channels:
Answers to the most-asked CyberGuy questions:
New from Kurt:
Copyright 2025 CyberGuy.com. All rights reserved.
Read the full article here